Norton Family Invalid Server Certificate. Please Check Your System Time and Try Again.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
by Kaushal Kumar Panday
Tools Used in this Troubleshooter:
- SSLDiag
- Network Monitor three.4/Wireshark
This fabric is provided for informational purposes only. Microsoft makes no warranties, limited or implied.
Overview
This certificate will help you in troubleshooting SSL problems related to IIS only. Client Certificates troubleshooting will not be covered in this document. Server Certificates are meant for Server Authentication and nosotros will be dealing just with Server Certificates in this document.
If the Customer certificates section is ready to "Require" and and then you run into issues, then please don't refer this certificate. This is meant for troubleshooting SSL Server certificates consequence only.
Information technology is important to know that every certificate comprises of a public key (used for encryption) and a private key (used for decryption). The individual key is known only to the server.
The default port for https is 443.
I am under the assumption the reader is well-versed in SSL Handshake and the Server Authentication procedure during the SSL handshake.
Clarification of the Secure Sockets Layer (SSL) Handshake:
https://support.microsoft.com/kb/257591
Description of the Server Hallmark Process during the SSL Handshake:
https://back up.microsoft.com/kb/257587
Scenarios
The post-obit error message is seen while browsing the website over https:

The outset thing that has to exist checked is whether the website is accessible over http. If it is not, there likely is a separate issue not covered here. Y'all volition need to take the website working on http first before continuing with this troubleshooter.
Now let'southward assume the website is accessible over http and we become the above error when trying to browse over https. The problem is seen because the SSL handshake failed and hence the error message was seen. At that place could be many reasons. We will follow a step-past-step approach to solve this problem.
Scenario ane
Check if the server document has the private cardinal respective to it. Refer the below picture:
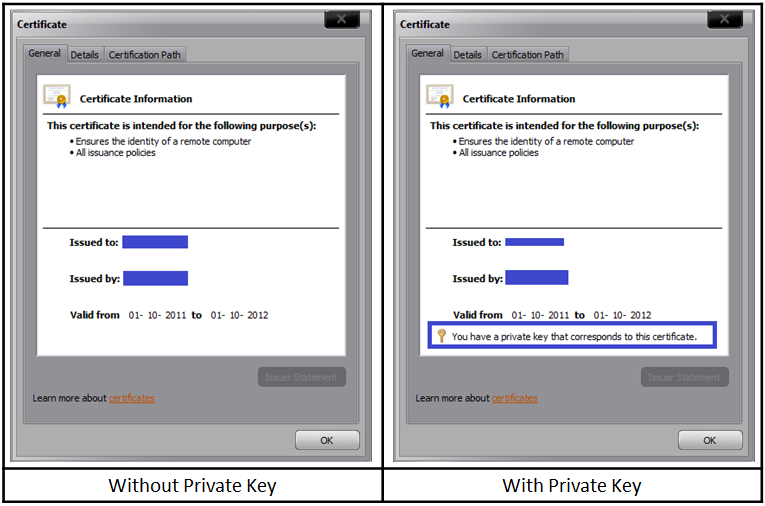
If private key is missing, then yous demand to go a certificate containing the private key, which is essentially a .PFX file. At that place is a command that nosotros could try to run in order to associate the private key with the certificate:
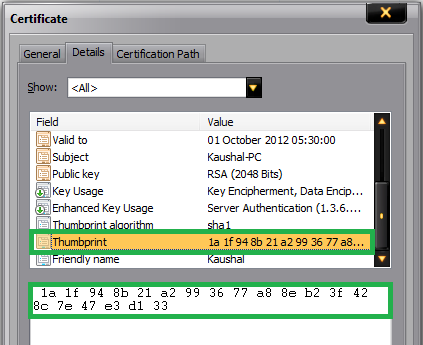
C:\>certutil –repairstore my "1a 1f 94 8b 21 a2 99 36 77 a8 8e b2 3f 42 8c 7e 47 e3 d1 33" 
If the clan is successful, and then you lot would encounter the post-obit window:

Note: 1a 1f 94 8b 21 a2 99 36 77 a8 8e b2 3f 42 8c 7e 47 e3 d1 33 is the thumbprint of the certificate. Open the document and click on the details tab. Coil downward to find the thumbprint section. Select the thumbprint department and click on the text beneath. Do a "Ctrl+A" and then "Ctrl+C" to select and copy it. Below is a snapshot for your reference:
Annotation: This command doesn't succeed ever. If this fails, then you lot demand to go a certificate containing the individual cardinal from the CA. The file extension for a certificate containing private key is .pfx.
Scenario 2
We went pass the get-go hurdle and now we take a server document containing the private key installed on the website. Withal, nosotros still get the same error as in a higher place. The website is still non accessible over https.
The SSLDiag tool comes in handy here.
Windows Server 2003:
Download X64
Download X86
For IIS 7 and IIS 7.5, utilize vijaysk's SSL Diagnostics tool. Below is the link:
https://blogs.msdn.com/b/vijaysk/archive/2009/09/20/ssl-diagnostics-tool-for-iis-7.aspx
Install the tool and run it on the server. If you have a certificate containing private primal and still non able to access the website, then y'all may want to run this tool or check the system issue logs for SChannel related warnings/errors.
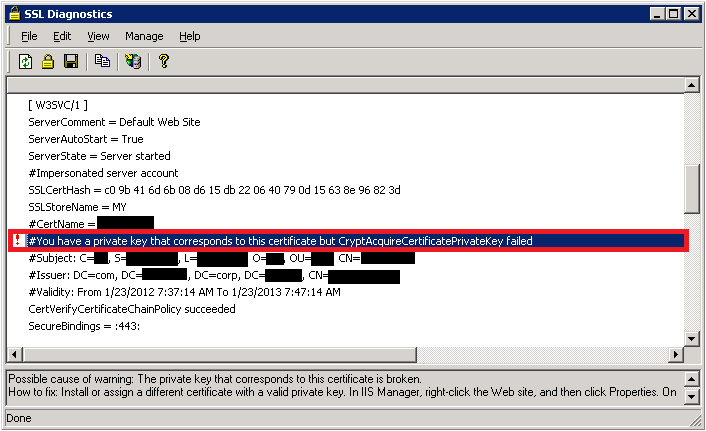
While running the SSLDiag tool y'all may get the post-obit error:
You have a private central that corresponds to this certificate but CryptAcquireCertificatePrivateKey failed
In that location will also be a SChannel warning in the system consequence logs every bit shown below:
| Event Type: Error |
|---|
| Event Source: Schannel |
| Result Category: None |
| Event ID: 36870 |
| Date: 2/xi/2012 |
| Time: 12:44:55 AM |
| User: N/A |
| Computer: |
| Description: A fatal error occurred when attempting to access the SSL server credential individual key. The fault lawmaking returned from the cryptographic module is 0x80090016. |
This event/error indicates that there was a problem acquiring certificate's private key. And so permit's try the below steps one by one:
-
Firstly, verify the permissions on the machinekeys folder as per the KB Article: https://support.microsoft.com/kb/278381. All the private keys are stored within the machinekeys binder, so we need to ensure that we have necessary permissions.
-
If the permissions are in place and if the result is still not fixed. Then it must be a problem with the certificate. It may have been corrupted (Y'all may come across an fault code of 0x8009001a in the SChannel effect log).
Upshot Type: Error Result Source: Schannel Result Category: None Event ID: 36870 Date: 2/xi/2012 Time: 12:44:55 AM User: N/A Computer: A fatal fault occurred when attempting to admission the SSL server credential private key. The error code returned from the cryptographic module is 0x8009001a. -
Nosotros will examination if the website works with a test document. Take a back-up of the existing document and then replace it with a self-signed document. Try accessing the website via https. If it works then the certificate used earlier was corrupted and information technology has to be replaced with a new working certificate.
-
Sometimes the problem may not be with the certificate but with the issuer. You may see the following error in SSLDiag:

CertVerifyCertificateChainPolicy will fail with CERT_E_UNTRUSTEDROOT (0x800b0109), if the root CA certificate is non trusted root.
To fix this add the CA's certificate to the "Trusted Root CA" store under My calculator account on the server.
-
You may also get the following error:
CertVerifyCertificateChainPolicy returned error -2146762480(0x800b0110).
If the above error is received then we demand to check the usage type of the certificate. Open the certificate, click on the "Details" tab then click on "Edit Properties…" push button. Under General tab brand sure "Enable all purposes for this document" is selected and most importantly "Server Authentication" should exist nowadays in the list.

Scenario 3
The first two steps bank check the integrity of the document. One time we have confirmed that there are no issues with the certificate, a big trouble is solved. Merely, what if the website is still not accessible over https. Check the HTTPS bindings of the website and determine what port and IP it is listening on. Y'all could run the post-obit command to ensure no other procedure is listening on the SSL port used by the website.
netstat -ano" or "netstat -anob If at that place is another process listening on that port and so bank check why that procedure is consuming that port. Endeavour changing the IP-Port combination to bank check if the website is accessible or not.
Scenario four
By now we are sure that we have a proper working certificate installed on the website and there is no other process using the SSL port for this website. Yet, I even so get "Page cannot be displayed" error while accessing over https. When a client connects and initiates an SSL negotiation, HTTP.sys looks in its SSL configuration for the "IP:Port" pair to which the client continued. The HTTP.sys SSL configuration must include a document hash and the proper noun of the certificate store before the SSL negotiation will succeed. The problem may be with the HTTP.SYS SSL Listener.
-
The Certificate hash registered with HTTP.SYS may be NULL or information technology may contain invalid GUID. Execute the following from a command prompt:
IIS half-dozen: "httpcfg.exe query ssl" IIS 7/seven.5: "netsh http show ssl"Below is a sample of a working and not-working scenario:
Working scenario:
Configuration Setting IP 0.0.0.0:443 Hash Guid {00000000-0000-0000-0000-000000000000} CertStoreName MY CertCheckMode 0 RevocationFreshnessTime 0 UrlRetrievalTimeout 0 SslCtlIdentifier 0 SslCtlStoreName 0 Flags 0 Non-working scenario:
Configuration Setting IP 0.0.0.0:443 Hash c09b416d6b 8d615db22 64079d15638e96823d Guid {4dc3e181-e14b-4a21-b022-59fc669b0914} CertStoreName MY CertCheckMode 0 RevocationFreshnessTime 0 UrlRetrievalTimeout 0 SslCtlIdentifier 0 SslCtlStoreName 0 Flags 0 The Hash value seen above is the Thumbprint of your SSL certificate. Notice, that the Guid is all zippo in a non-working scenario. You may see the Hash either having some value or blank. Even if we remove the certificate from the web site, then run "httpcfg query ssl", the website will still list Guid as all 0'due south. If you lot see the GUID as "{0000...............000}, so there is a trouble.
We need to remove this entry past running the command:
httpcfg delete ssl -i "IP:Port Number"For case:
httpcfg delete ssl –i 0.0.0.0:443 -
Delete any entries in the IP Listen list.
To make up one's mind whether any IP addresses are listed, open a command prompt, and and so run the post-obit command:
IIS 6: httpcfg query iplistenIIS 7/seven.5: netsh http show iplistenIf the IP Heed list is empty, the command returns the following string:
HttpQueryServiceConfiguration completed with 1168.If the command returns a list of IP addresses, remove each IP address in the list by using the following command:
httpcfg delete iplisten -i x.x.10.xNotation
restart IIS afterward this via control "cyberspace terminate http /y"
Scenario 5
After all this if y'all are all the same unable to scan the website on https, then capture a network trace either from the customer or server. Filter the trace by "SSL or TLS" to await at SSL traffic.
Below is a network trace snapshot of a not-working scenario:

Working scenario:

Well, this is definitely now how you expect at a network trace. You demand to aggrandize the frame details and see what protocol and cipher was chosen by the server. Select "Server Hello" from the clarification to go those details.
In the non-working scenario, the client was configured to use TLS ane.1 and TLS 1.2 only. However, the spider web server was IIS half dozen, which can support until TLS one.0 and hence the handshake failed.
Practise cheque the registry keys to determine what protocols are enabled or disabled. Hither's the path:
HKEY_LOCAL_MACHINE\Organization\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols The "Enabled" DWORD should exist gear up to "1". If "0" then the protocol is disabled.
For example, SSL 2.0 is disabled by default.
Scenario 6
If everything has been verified and if you are yet running into issues accessing the website over https, then it most likely is some update which is causing the SSL handshake to fail.
Microsoft has released an update to the implementation of SSL in Windows:
MS12-006: Vulnerability in SSL/TLS could allow information disclosure: January ten, 2012 There is potential for this update to affect customers using Internet Explorer, or using an awarding that uses Internet Explorer to perform HTTPS requests.
At that place were actually 2 changes made to address information disclosure vulnerability in SSL 3.0 / TLS i.0. The MS12-006 update implements a new behavior in schannel.dll, which sends an actress tape while using a common SSL chained-block nix, when clients request that beliefs. The other alter was in Wininet.dll, role of the December Cumulative Update for Internet Explorer (MS11-099), and so that IE will asking the new beliefs.
If a problem exists, it may manifest as a failure to connect to a server, or an incomplete request. Cyberspace Explorer nine is able to display an "Cyberspace Explorer cannot display the webpage" mistake. Prior versions of IE may simply brandish a bare folio.
Fiddler does not apply the extra record when it captures and forrard HTTPS requests to the server. Therefore, if Fiddler is used to capture HTTPS traffic, the requests volition succeed.
Registry keys
Every bit documented in https://support.microsoft.com/kb/2643584, there is a SendExtraRecord registry value, which can:
- Globally disable the new SSL behavior
- Globally enable it, or
- (Default) enable it for SChannel clients that opt in to the new beliefs.
For Internet Explorer and for clients that consume IE components, there is a registry key in the FeatureControl section, FEATURE_SCH_SEND_AUX_RECORD_KB_2618444, which determines whether iexplore.exe or whatever other named application opts in to the new behavior. By default this is enabled for Internet Explorer, and disabled for other applications.
Other Resource
- Description of the Secure Sockets Layer (SSL) Handshake
- Clarification of the Server Authentication Process During the SSL Handshake
- Fixing the Beast
- Taming the Animal (Browser Exploit Against SSL/TLS)
- SSL CERTIFICATE FILE EXTENSIONS
- Support for SSL/TLS protocols on Windows
- Troubleshooting SSL related issues with IIS
- PRB: Cannot visit SSL sites after you enable FIPS compliant cryptography
- HTTP one.1 host headers are not supported when you lot employ SSL
- Configuring SSL Host Headers (IIS vi.0)
Source: https://docs.microsoft.com/en-us/iis/troubleshoot/security-issues/troubleshooting-ssl-related-issues-server-certificate
Belum ada Komentar untuk "Norton Family Invalid Server Certificate. Please Check Your System Time and Try Again."
Posting Komentar